SharePoint High-Trust Authorization Prerequisite
Attention! If the security model selected from the Prerequisites is not the High Trust Model this section can be skipped.
Important Note
-
Setting up SharePoint High-Trust Authorization is only required when using Document Library Tagging.
-
Document Library Tagging requires deploying the SharePoint Add-In App.
-
If the Add-In App is not being deployed this section can be skipped.
Tip: Below is a helpful link to prepare your SharePoint Environment for SharePoint Add-Ins:
- The BA Insight AutoClassifier SharePoint Add-in is developed as a high-trust provider-hosted SharePoint add-in that is installed to an on-premise SharePoint farm.
- A high-trust add-in uses a certificate instead of a context token to establish trust.
- Using a Farm Administrator, you establish the trust between SharePoint and the BA Insight AutoClassifier SharePoint Add-in by using Windows PowerShell cmdlets and a certificate.
Below, the Farm Administrator makes the certificate of the high-trust add-in a trusted root authority in SharePoint as well as a trusted token issuer.
Note: When there is a hierarchy of certificate issuing authorities behind a web application's certificate, all the certificates in the chain must be added to SharePoint's list of trusted root authorities.
-
In case you are using a self-signed certificate, there is no certificate chain and only the web application's certificate must be added to the list of root authorities.
Prepare SharePoint On-Premise for High-Trust Authorization
To use the On-Premise SharePoint Add-In your SharePoint farm must be configured for High-Trust Authorization.
Configuring SharePoint requires three Service applications to be installed and configured:
- App Management Service Application
- User Profile Service
- Microsoft SharePoint Foundation Subscription Settings Service
How to Verify or Add Service Applications
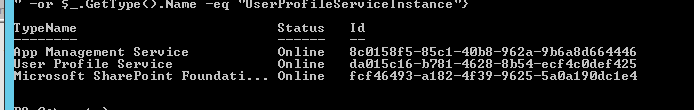
To determine if the SharePoint Farm is ready, look under Application Management to determine if each service is installed and running. Alternatively, run the following PowerShell command as a SharePoint Administrator:
Get-SPServiceInstance | where{$_.GetType().Name -eq "AppManagementServiceInstance" -or $_.GetType().Name -eq "SPSubscriptionSettingsServiceInstance" -or $_.GetType().Name -eq "UserProfileServiceInstance"}
- App Management Service
If the App Management service is missing, create it through SharePoint Central Admin Application Management. -
User Profile Service
If the User Profile service is missing create it through SharePoint Central Admin Application Management.Note: You must have at least one valid user profile.
If not, you must synchronize to AD to manually create a profile.
-
Microsoft SharePoint Foundation Subscription Settings Service
-
If the Microsoft SharePoint Foundation Subscription Settings service is missing, it can be created with the following PowerShell commands:
$account = Get-SPManagedAccount "domain\user"$appPoolSubSvc = New-SPServiceApplicationPool -Name SettingsServiceAppPool -Account $account
$appSubSvc = New-SPSubscriptionSettingsServiceApplication -ApplicationPool $appPoolSubSvc -Name SettingsServiceApp -DatabaseName SettingsServiceDB
$proxySubSvc = New-SPSubscriptionSettingsServiceApplicationProxy -ServiceApplication $appSubSvc
Set-SPAppSiteSubscriptionName -Name "addin" -Confirm:$false -
- Check and verify your add-in domain
Run the following command from PowerShell (this is a virtualDomain where Apps reside)
Get-SPAppDomain
-
If the app add-in domain is not set, Create your app add-in domain:
-
Run the following PowerShell command (default is bainsightaddins.com):
Set-SPAppDomain "<your add-in domain>"
-
- Start or Recycle the Timer Service
- Validate the Admin and Timer Service are running.
- Run SharePoint Management Shell as an administrator using the following commands:
net start spadminv4
net start sptimerv4
- Enable OAuth over HTTP - (done in non-production environment only)
If your SharePoint runs on HTTP, run the following commands:$serviceConfig = Get-SPSecurityTokenServiceConfig
$serviceConfig.AllowOAuthOverHttp = $true
$serviceConfig.Update()