About Ricoh Android Device SSL Configuration
Secure Sockets Layer (SSL) is a standard security protocol for establishing an encrypted link between a server and a client. It allows sensitive data to be transmitted securely. Browsers and secured web servers have the capability of interacting with each other, but require an SSL certificate to establish a secure connection. SSL-secured websites begin with https.
Understanding SSL Certificates
A certificate is required for all SSL-related transactions to ensure secure data transmissions and prevent eavesdropping. There are 2 types of SSL certificates.
Self-Signed CA Certificate
A Self-Signed CA certificate is authenticated by a trusted Certificate Authority authorized to issue them. Certificate Authorities are trusted resources that meet all the requirements that have been set for issuing certificates. They have the appropriate safeguards in place to prevent misuse and other types of fraudulent behavior. It is recommended that a Self-Signed CA certificate is used for secure communication between the AccuRoute Server and Ricoh (Android) devices.
Self-Signed Certificate
A Self-Signed certificate is issued by the individual using it with their own software. It may be used on intranets or testing environments; however, if used on the Internet, they generate browser warnings that could dissuade potential customers from using a website. Although, this type of certificate provides encryption, it does not provide authentication and it is not recommended for secure communication between the AccuRoute Server and Ricoh (Android) devices.
Note: Installation of the Self-Signed certificate is not allowed on the device’s trust store making it impossible for the client to ever trust the server’s certificate.
Before you begin
The following installations and setup are required in the order specified before SSL configuration can take place.
AccuRoute Server installation
Note: See the AccuRoute Server Install Guide for more information.
Device Client installation on the AccuRoute Server
- Using File Explorer, go to Program Files (x86) > Upland AccuRoute > AccuRoute > Clients > DeviceClient.
- Run setup as an administrator.
Note: The Device Client installation may have occurred during the server installation. The steps are provided in the event you have added devices that were not part of the original configuration.
Ricoh Device Client installation on the AccuRoute Server
- Using File Explorer, go to Program Files (x86) > Upland AccuRoute > AccuRoute > Clients > Ricoh ESA UDC.
- Run setup as an administrator.
AccuRoute Server to Ricoh device installation
- Start the AccuRoute Server Administrator.
- Right- click Devices. The Devices shortcut menu appears.
- Select New > Ricoh group and create the device group, if necessary.
- Right-click the Ricoh device group. The Device group shortcut menu appears.
- Select Install.
There are several CA resources that you can use to obtain Self-Signed CA certificates. It is recommended that you research and select a CA resource that works for you and your company.
In addition, you must determine whether you are going to use a CA resource to create your own Self-Signed CA certificate and Private key or have the CA resource create and provide you with the Self-Signed CA certificate and Private key.
Note: The following instructions refer to the use of OpenSSL for illustrative purposes only. You are not required to use OpenSSL. If you obtained your Self-Signed CA certificate and Private key from a CA resource, then you can proceed to Creating a Server certificate request.
What you need to do to configure SSL
Complete the steps in the order specified.
Creating a Self-Signed CA certificate and generating a Private key
Using a CA resource, you must create a Self-Signed CA certificate and generate a Private key.
Note: Refer to the documentation provided by your CA resource. The next series of steps use OpenSSL as an example and may not apply to your specific SSL configuration.
To create a Self-Signed CA certificate and generate a Private key
-
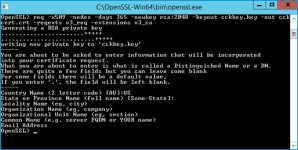
Download, open and run the OpenSSL.exe file as an Administrator.
-
Type or copy/paste the following command at the prompt to create a Self-Signed CA certificate, generate a Private key, and press Enter.
openssl req -x509 -nodes -days 365 -newkey rsa:2048 -keyout privateKey.key -out certificate.crt -reqexts v3_req -extensions v3_ca
Note: X.509 version 1 certificates are not allowed by some mobile platforms. Use the X.509 version 3 certificates instead. When creating Self-signed CA certificates, ensure that they are X.509 version 3 and have the following extension defined: basicConstraints = CA:TRUE.
-
Verify the certificate version and extensions, if necessary, by typing the following command and press Enter.
openssl x509 -in certificate.crt -text -noout
Note: Refer to the documentation provided by your CA resource for how to specify the required version and certificate extensions.
See the OpenSSL.exe file example below.
-
Type the following information that will be included in your certificate request and press Enter.
-
Country Name
-
State or Province Name
-
Locality Name
-
Organization/Company Name
-
Organizational Unit Name
-
Common Name
-
Email Address
Note: Some of these fields can be left blank. A Self-Signed CA certificate (certificate.crt) is created and a Private key (privateKey.key) is generated when you are done.
See also
SSL Configuration Server Certificate Request